Here is a tutorial on how to virtualize OPNSense on a Proxmox Hypervisor <3.
I decided to move away from a consumer router to an enterprisey router like OPNSense. The best way to get experience on a technology stack is to use it on production.
Potential Benefits
- Play with Intrusion detection/prevention systems
- More custom DHCP settings (per lease level dns, gateway)
- WAN Load balancing
- IPV6 NAT
- Scriptability
- Firewall Logs (You can see a lot)
- Unified experience on different hardware. I’m not bound to a specific manufacturer to buy routers (for my level of networking, if you go datacenter level its a different story)
Steps
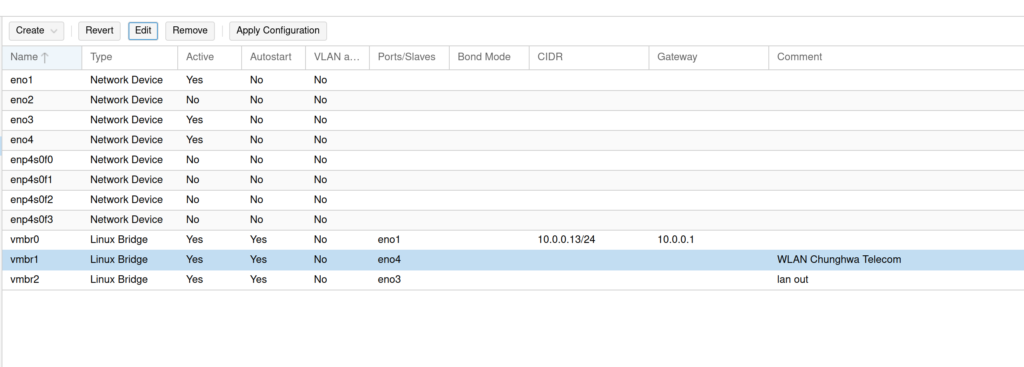
My host used for this tutorial has 4 ethernet ports. I wired them as following:
eno1 – default Proxmox Lan port
eno2 – empty
eno3 – LAN for OPNSense
eno4 – WAN for OPNSense
and I have 3 linux bridges:
vmbr0 — eno1 has CIDR for proxmox host IP address + gateway (LAN)
vmbr1 — eno4 (WLAN)
vmbr2 — eno3 (LAN)
Here is a screen shot as well:
My OPNSense VM has two network devices
net0 bridged to vmbr1 (WLAN)
net1 bridged to vmbr2 (LAN)
from here the configuration is pretty straight forward.
1) Manually choose LAN/WAN interfaces in terminal while doing the setup, auto discover failed for me.
2) Make sure that your DNS settings are the way you want them to be! I had to tweak some settings in the unbound DNS service page (forward DNS requests)
3) As with every new router, get a new lease from a client and check the results. My old router had hardcoded dns settings in DHCP leases. Consumer grade routers don’t really care if you want custom DNS or not.
I initially set this up in my test cluster, my main fear was wifi wouldn’t work as the way I want it to work, but it didn’t happen to be the case. You need to switch your access point into “AP Mode” to work with OPNSense router. In that configuration access point lets the clients connected to itself get DHCP lease from the OPNSense. The access point also has a LAN IP address where you can configure it’s security settings (Wifi password etc)
Next I want to try IPV6 NAT.